Ransomware attack should be a 'wake-up call' for governments
By Shelly Foster May 17, 2017Officials and experts on Sunday urged organizations and companies to update their operating systems immediately to ensure they aren't vulnerable to a second, more powerful version of the malicious software.
Security experts expressed alarm Friday over a fast-moving wave of cyberattacks around the world that appeared to exploit a flaw exposed in documents leaked from the US National Security Agency.
On affected computers, the WannaCry software encrypts files and displays a ransom message demanding $300 in bitcoin.
Here's a look at how malware and ransomware work and what people can do if they fall victim to attacks.
Japan's Chief Cabinet Secretary Yoshihide Suga said there weren't any concerns about damage in the country.
"It's this constant battle", Ryan O'Leary, vice president of WhiteHat Security's threat research center, said.
There are several factors in play. In most cases, they change the wallpaper of the computer and give specific instructions telling the user how to pay to recover their files. This morning, Europol Director Rob Wainwright told the BBC that the cyberattack is "unprecedented in its scale", and noted that it will likely continue as people return to work on Monday.
With an aim to prevent the cyber attack "WannaCry", the Ministry of Electronics and Information Technology (MeitY) said that it has already activated a "preparedness and response mechanism".
At least one strain of the ransomware has proven especially vicious.
Microsoft Blasts the CIA and NSA for "Stockpiling" Software Vulnerabilities
Problems with the radiology system in the Western Isles was affecting staff's ability to share images with mainland health boards. If you're not on a work network that already has security, consider installing some form of security program on your computer.
Experts said that even as the spread of the attacks apparently has been stymied, its full ramifications are not yet known because the virus may be lurking still on computers around the world.
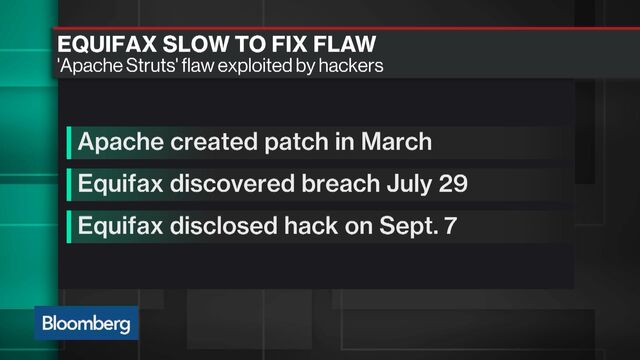
One of the biggest-ever ransomware attacks continues to take computers hostage. A hacking group released details on the exploit in April when they published a collection of spy tools allegedly used by the National Security Agency online. This one worked because of a "perfect storm" of conditions, including a known and highly unsafe security hole in Microsoft Windows, tardy users who didn't apply Microsoft's March software fix, and malware created to spread quickly once inside university, business or government networks. Do not enable macros, cybersecurity company Symantec says.
Grafi said his firm has been contacted by companies that are scrambling to avoid potential pitfalls. Many may click infected email attachments or bad links and spread the virus further. Microsoft had "patched", or fixed it, in updates of recent versions of Windows since March, but many users did not apply the software fix.
Gas stations: State-run media in China reported that some gas stations saw their digital payment systems shut down, forcing customers to bring cash.
James Clapper told ABC's "This Week" on Sunday that he expects similar attacks to become a growing problem in the future.
In China, "hundreds of thousands" of computers at almost 30,000 institutions and organisations were infected by late Saturday, according to Qihoo 360, one of China's largest providers of antivirus software. He further said that our banks may be affected in a couple of hours. In all, 150 countries have reported compromised computer systems.
"This exploit is named as ETERNALBLUE", an advisory issued by the CERT-In, accessed by PTI, said. Organizations had two months to update their Microsoft products, which would have protected their systems. The affected groups include the United Kingdom hospitals, FedEx, a Spanish telecom, the Russian Interior Ministry and much more. The statement said antivirus systems are working to destroy it.
Spain's Telefonica, a global broadband and telecommunications company, was among the companies hit. He said the situation was under control.
As the disruptions rippled through hospitals, doctors' offices and ambulance companies across Britain on Friday, the health service declared the attack as a "major incident", a warning that local health services could be overwhelmed by patients. You may lose some data, but it's a lot better than losing access to all of your files. The attack on Britain's NHS was potentially the most devastating as thousands of patients' appointments were cancelled, ambulances rerouted, records lost and chaos followed, despite the warnings delivered, some as recently as previous year, on the vulnerability of outdated systems. The British Home Secretary said most of the NHS systems were back to normal by midday Saturday.
You may also like...
-
-
What is ransomware and how can you protect yourself from it?
-
-
-
-
-
-
-
/cdn0.vox-cdn.com/uploads/chorus_image/image/54768923/usa_today_10053872.0.jpg) Joe Maddon upset about call against Cubs at second base
Joe Maddon upset about call against Cubs at second base
-
Advertisement
-
Leadership
 National Hockey League playoffs: Kessel gets Penguins on even terms with Senators
National Hockey League playoffs: Kessel gets Penguins on even terms with Senators
May 17, 2017Marcus Smart: Marcus Smart steps up in Game 7 win
May 16, 2017 HTC's 2017 flagship U11 woos audiophiles and bundles Alexa
HTC's 2017 flagship U11 woos audiophiles and bundles Alexa
May 16, 2017Syrian Kurdish forces to push on IS capital this summer
May 15, 2017Spurs face quick turnaround before conference finals
May 14, 2017 -
-
The Latest
-
 | Sep 15, 2017
| Sep 15, 2017
Has Winter come to Bitcoin with exchange closures in China ?
-
 | Sep 15, 2017
| Sep 15, 2017
-
 | Sep 14, 2017
| Sep 14, 2017
-
 | Sep 13, 2017
| Sep 13, 2017
North Korean hackers are 'stealing bitcoin' to evade sanctions
-
/cdn.vox-cdn.com/uploads/chorus_image/image/56550159/463788546.0.jpg) | Sep 12, 2017
| Sep 12, 2017
Southwest Airlines canceled hundreds of flights to and from Atlanta
-
 | Sep 07, 2017
| Sep 07, 2017
With Deondre Francois Out, Florida State's Season Just Went Off The Rails
-
-
-
 | May 15, 2017
| May 15, 2017
Bison softball team to play defending national champion Oklahoma
-
 | May 14, 2017
| May 14, 2017
Moms reveal what they really want for Mother's Day
-
-
- | May 07, 2017
-
 | April 30, 2017
| April 30, 2017
Trump's gyrations on NAFTA cause a flurry of head-scratching
-
Top Tags
Copyright © 2017 voiceherald.com - Voice Herald | All Rights Reserved



